How To Install X Server on a VPS (with VNC access)
This guide is intended to provide those users who desire it instructions on how to install a graphical user environment on their VPS. Because the usual method of access your VPS (SSH) does not support a graphical environment, we will also install a way of doing so, called VNC. VNC is an open-source desktop sharing protocol allowing, among many other things, remote access to the GUI of a system. It is very similar in function to the Terminal Services functionality on Windows.
Before we begin, we would like to caution users that a graphical user environment such as the X server (X windows) consumes significantly more resources than a typical SSH-based access system, and as such is not recommended for use in an environment where resources are scarce. We also do not recommend running a GUI on a server with any less than 512MB of memory.
Installing the Components
Our VPS images are intended to be very minimal to allow the most user customization, so you must install the full group packages for Xwindows and Gnome (the default window manager for most operating systems).
Use SSH to log in to your server and run the following:
For CentOS:
yum groupinstall "X Window System" "GNOME Desktop Environment" tigervnc-server
For Ubuntu (as root):
apt-get install ubuntu-desktop gdm vnc4server
For Debian (as root):
apt-get install xorg gdm gnome vnc4server
You will also need a VNC viewer for your PC. If you are on Microsoft Windows, you can try one of the free VNC viewers such as RealVNC Free Version. For Mac, we reccomend the open source project Chicken of the VNC.
Running VNC Server
Out of the box, the X server should come configured properly. We will however need to configure the VNC server to start automatically as well as start a new X server session when it is started as well.
First, we'll make sure VNC is working OK:
vncserver :1
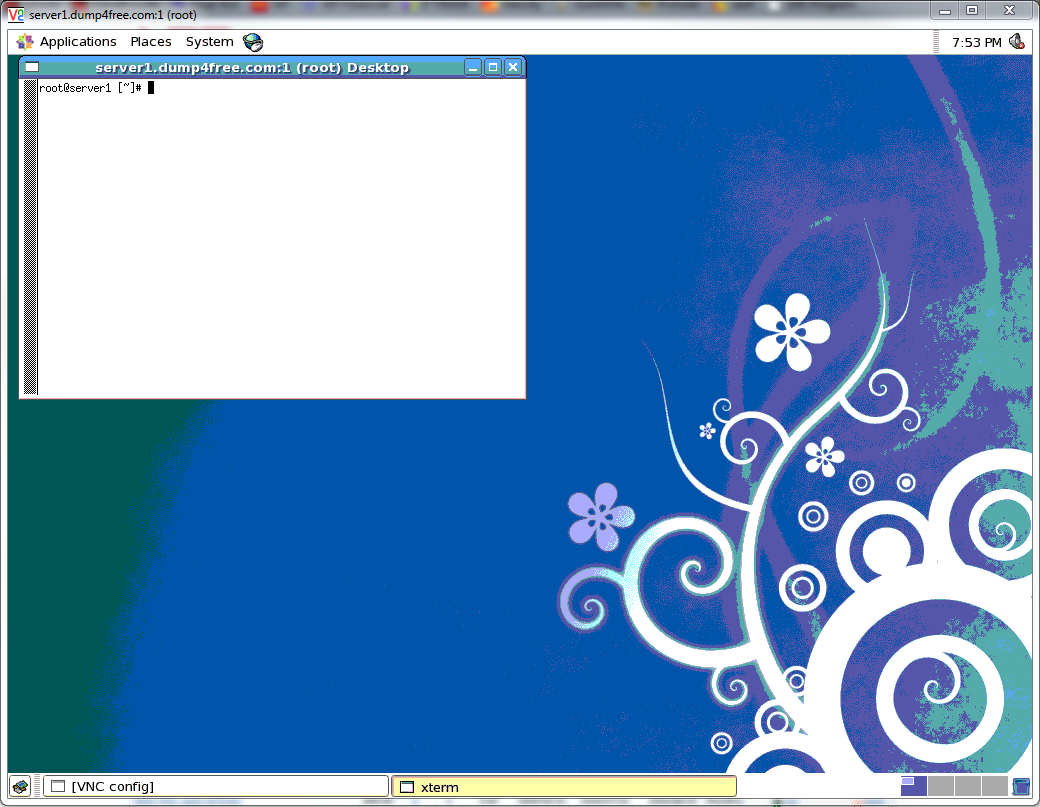
This will start the VNC server for the first time, create some configuration files, and start the VNC server listening on port 5091 (make sure to open this port in your firewall if necessary). You can now use your VNC viewer to connect to your server to make sure it is working properly. You can use the syntax hostname.domain.com:1 to connect to the server.
Running X Server
Once you have logged in for the first time, you will notice VNC only launches an xterm window with a very basic interface by default. We want to change its configuration to start a Gnome graphical environment when launched so we have a nice GUI to work with.
What we need to do is first stop the running VNC server:
vncserver -kill :1
Next we need to edit /root/.vnc/xstartup (or /home/user if you're running the server as a regular user) and modify the final line in the file, which should read twm & to the following (note the last line):
#!/bin/bash # Uncomment the following two lines for normal desktop: # unset SESSION_MANAGER # exec /etc/X11/xinit/xinitrc [ -x /etc/vnc/xstartup ] && exec /etc/vnc/xstartup [ -r $HOME/.Xresources ] && xrdb $HOME/.Xresources xsetroot -solid grey vncconfig -iconic & xterm -geometry 80x24+10+10 -ls -title "$VNCDESKTOP Desktop" & unset SESSION_MANAGER gnome-session &
If this file doesn't exist, create it, and make sure it is executable (chmod 0777).
Once done, we can restart our VNC server:
vncserver :1
Now you can log in as you did before, however this time you will be presented with a Gnome Desktop environment!
Starting on Boot
If you would like your VNC server to start with the system boot, we will need to modify the init startup scripts. For CentOS:
chkconfig vncserver --levels 2345 on
For Debian/Ubuntu, the VNC server should be automatically configured to start on boot. If not, you may need to update the rc scripts:
update-rc.d vnc4server defaults
Securing VNC
By default, VNC only encrypts the initial password communication then results to unencrypted transmission of the data stream. This can lead to problems if someone is able to sniff your network traffic, as could be the case communicating over the 'net with your VPS. To secure VNC, we will use an SSH tunnel to encrypt the VNC traffic:
http://www.cs.arizona.edu/computing/access/x11vnc.html